Certified Oracle Cloud Infrastructure (OCI) Consultants

SkillBuilders can design, provision, mentor and if needed, support your OCI environment.
Design: We can plan an APEX hosting cloud environment appropriate for your requirements in terms of scalability, fault tolerance, and security. There are many possibilities at various price points, including options for migrating existing applications to OCI from on-premises or third party cloud environments.
Provisioning: The environment can be built in our OCI account or the client’s. When running in SkillBuilders’ cloud, we take complete responsibility for provisioning, and the client would not usually have or require access to OCI administration functions. In the client’s cloud, we can build and document the environment, then hand over to the client for use.
Mentor: We run formal instructor-led courses on OCI, database, and system administration; also APEX, SQL, and PL/SQL development. An approach some clients find helpful is where we build the environment or application with the client, accomplishing the necessary skills transfer during the configuration and development process.
Support: There are various options for continuous support services following commissioning a system. Support can be reactive or proactive, with different levels depending on the demands of the application.
Case Study
Pharma/Biotech Marketing Firm – OCI Environment Provisioning, Oracle Database and APEX Stack Configuration, Plan and Support Production Go-Live
The assignment, delivered on-time and on-budget in Q1 of 2021, was to construct a secure, scalable, production-ready Oracle APEX environment in the Oracle Cloud (OCI), install an existing APEX app and coordinate a go-live.
Unlike the existing POC environment, the new OCI environment, and the APEX stack, needed to be a robust, scalable, and secure environment, configured using best practices for internet facing web applications. Security was a particular concern given the nature of the data being processed.
The existing application (an APEX user interface with connections to various external systems) was running fine with one compute node for the web tier and a second compute node running the database. Public access was through a load balancing router, with both compute nodes on a public subnet. This architecture was functional, but it lacked fault tolerance and is vulnerable to attack (DDOS and others).
SkillBuilders replaced it with the following architecture:
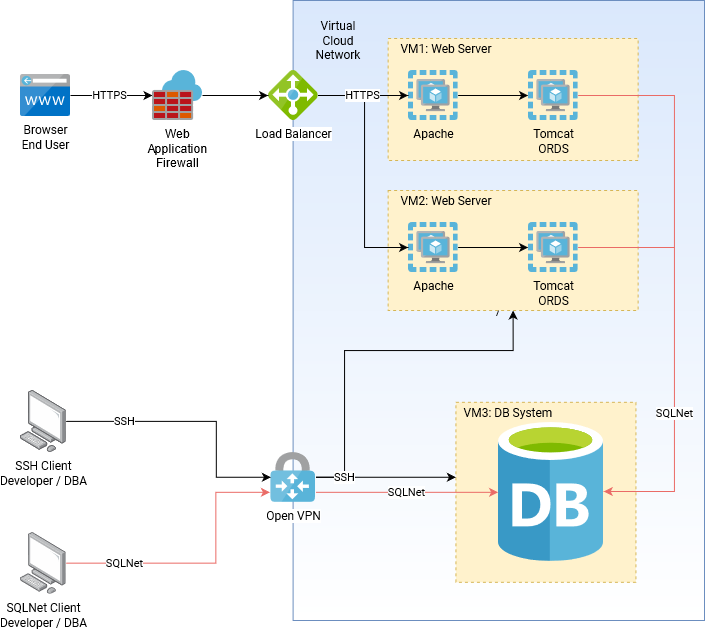
VM1 and VM2 are compute nodes on a private subnet running identical web tiers. This gives redundancy, not only for failure but more importantly so that reconfigurations can be done with zero downtime. VM3, also on the private subnet, is a compute node running the database. Calls to external systems from the application and the database go out through a NAT gateway (not shown in the graphic). The load balancing router is on a public subnet, configured to monitor the two web tier servers and spread requests across them. Also on the public subnet is another compute note, configured as an OpenVPN server. This provides access for developers and administrators to the nodes on the private subnet with ssh and SQL*Net. Within the virtual cloud network, all traffic is controlled with point-to-point routing, port filtering, and of course firewalls on each node. The final touch for security is the Web Application Firewall, which is where we deployed the web site’s digital certificate. The only downtime during the deployment was relocating the database to VM3. The source database was in fact a PDB, so we accomplished this with a network clone operation, complicated somewhat by the fact that the old environment was OCI “classic”.
This environment has now been running in production for several months with zero downtime.
Contact gary@skillbuilders.com




